HEXA OSINT CTF V2 Write-up
The HEXA OSINT CTF V2 took place online from January 27 to 29 2023. For 48 hours, the contestants
investigated a new case following the one from the first edition.
This is the write-up written by those who created the challenges, in which we will provide you the solutions
that we imagined when we created the challenges. We will also show you the hidden information that could
help solve the case.
Introduction
Welcome back
Dear agents,
You provided an outstanding work with the Manipar case just over a year ago. This
group of activists, who met on Erasmus, stole data from sensitive sectors (bank,
healthcare, military), to resell them to the highest bidders.
With their arrest, this case is therefore closed. However, their leader, Lucilhe
Dumarquais disappeared during a transfer. She intended to reveal more information
about collaborating criminal organizations. Since then, there is no trace of her.
The investigation reached a dead end. The minister asked to carry on. Given your
knowledge of the case, you are assigned to take over and understand this
disappearance.
We will ask you to provide every answer onto that format:
HEXA{challenge_answer} (case insensitive, dash/underscore/space accepted, no
accent).
If you understood the instructions, write HEXA{Briefing_OK}.
This introduction sets the context and exposes two very important pieces of information: The starting point of
the investigation is the disappearance of Lucilhe Dumarquais, and Lucilhe was selling sensitive information
before being arrested.
As written in the challenge statement, the flag was HEXA{Briefing_OK}.
Once the challenge was solved, 4 new challenges were unlocked: Hijacking, Fast and furious, The law firm and
The intruder, divided into three branches: Action Man, The Lawyer and The intruder. For the sake of clarity, we
will describe all the challenges branch by branch
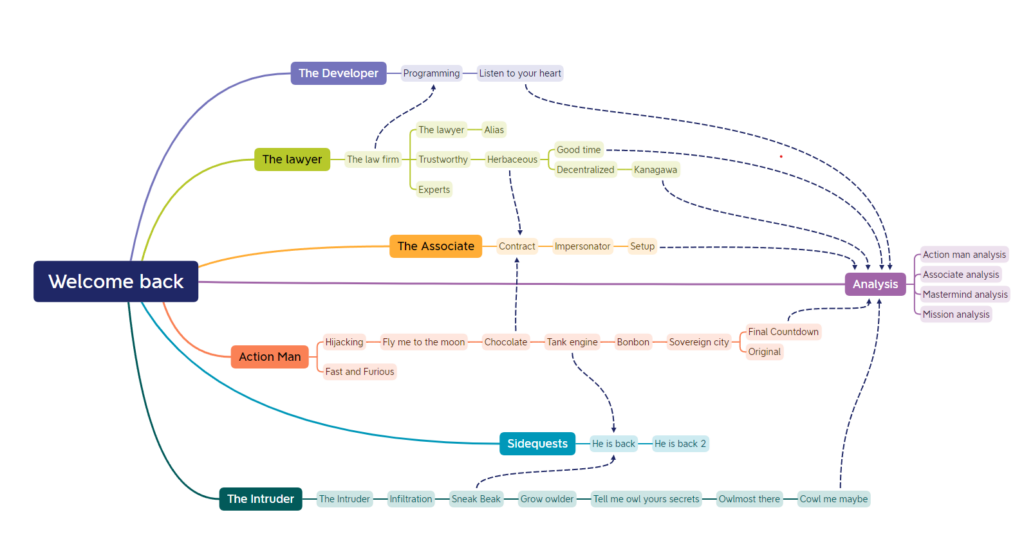
Action man
Hijacking
The convoy transporting Lucilhe from « Maison d’arrêt de Versailles » was hijacked
on the 30th of November 2022. She has not been seen since and her case file is
incomplete. A tiny mistake has been made: the picture of the convoy’s destination
was provided but not the place’s name. Please begin by completing the file with
the name of this convoy’s destination.Format: HEXA{french_destination_name}

This first challenge of GEOINT is simple when you know Google Lens. Using it on the picture allow us to
recognize the HEXA{Tribunal_judiciaire_de_Versailles}.
Fast and Furious
A witness saw a patrol wagon driving at top speed. We think it was the one
carrying Lucilhe.
Can you retrieve the road’s name where the picture was taken from?Format: HEXA{french_street_name}

As we can see on the signs, the picture has been taken near « Vélizy 2 »: a mall near Versailles, the city where
Lucilhe escaped. The research area can therefore be narrowed:

Another information available is « hotel de ville ». Let us search this on Google Maps:

The most likeable is the « Vélizy hotel de ville » (center of the picture), so the intersection right underneath may
match. A google street map verification allows to check the information and we find HEXA{Avenue de
l’EUROPE}.
Fly me to the moon
We found the place where they were hiding after the hijacking. The attachments are
evidences we found there. Can you find the city they were heading to?Format: HEXA{city}
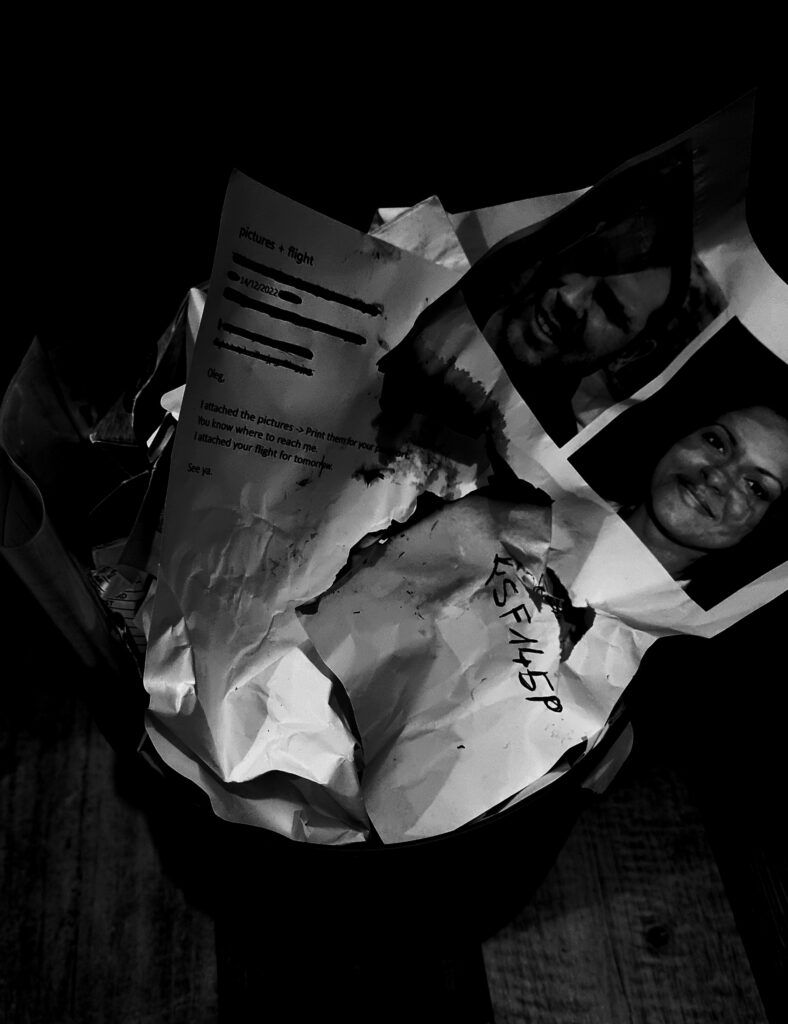
This challenge is unlocked after Hijacking. In this picture there is a printed email talking about a flight,
alongside a written flight number « FSF145P ». The email contains a date: 14/12/2022 and mentions a flight for
« tomorrow ». Searching for the number on google and looking for on the right date leads to:
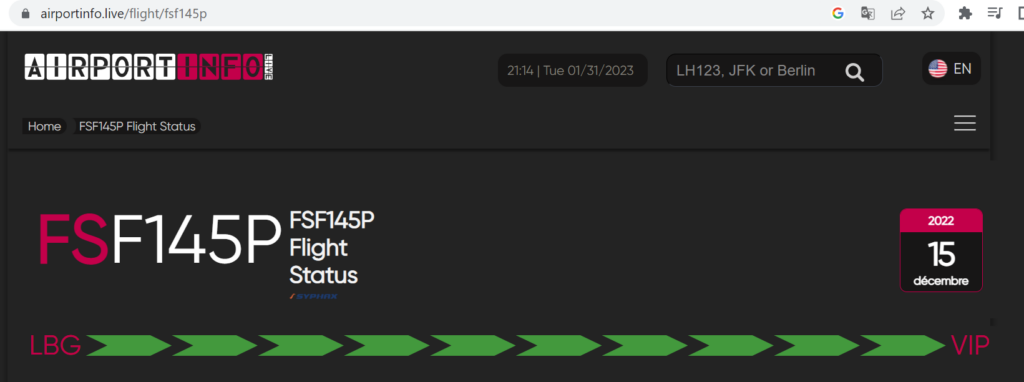
The flight did go to VIP, searching for airport code VIP gives the answer HEXA{Payerne}:

It is also interesting to note the presence of two pictures, probably from the travelers.
Chocolate
Using the data we found on the previous safehouse, we managed to retrieve a
message sent weeks ago: « We arrived. It was necessary to use public transports,
all the taxis were taken. Hurry up, I feel uneasy waiting here ». This picture was
attached. Find the street where they are waiting.Format: HEXA{street_name}

So, in the previous challenge Fly me to the moon the action man took a flight to Switzerland. Let us analysis
the picture to find some interesting details:
- Tramway line
- Swiss flag in a store logo
- A restaurant, with « alle wol » letters visible
With the lead from the previous challenge and the Swiss flag we will suppose that we are looking for a place
in Switzerland. Action man is « uneasy waiting here » and the presence of the tram line leads us to a big city.
Only four cities in Switzerland have a functional tramway: Zurich, Bâle, Genève, Berne. That is a good guess to
take since we are looking for someone who used public transports. Dorking « alle wol Zurich » allows us to find
Bierhalle Wolf, the restaurant in HEXA{Limmatquai}, Zurich, where the picture has been taken.
Tank engine
We found evidence of their passage in a safehouse in the previous location you
have found. The most interesting one is a phone with a received message weeks ago
from a contact named « action man »: « We took a direct train connection from Zurich.
The journey takes 03:07. Our contact also confirmed the appointment. » In which
city did this appointment take place?Format: HEXA{city}
After their passage in Zurich, we discovered in the previous challenge Chocolate, they took a direct train
connection from Zurich to an unknown place. Dorking « direct train connection » lead us to Direkt Bahn Guru, a
website where you can see direct train connections from a given place. Selecting Zurich Main station, we can
see that HEXA{Cadenazzo} is the right place. https://direkt.bahn.guru/?origin=8503000
Bonbon
Another message with a picture was received from « action man » on the phone
previously found, but more recently: « We drove few hours and took the boat. We
arrived at the safehouse yesterday. We are about to head East. Still 142km to go
until the airport near the fortress. Will be there for boarding in 3 days as
planned. » Can you find the airport where they boarded?Format: HEXA{airport_name}

After the Tank engine, they managed to reach Greece. On this new challenge, a picture is attached but it is
difficult to find any clue on it. By searching in the metadata we find an exact location in Crete:

There are several airports around:

But one of them to the east seems like a good candidate for what we are looking for. We will verify our theory
by tracing the route on Google Maps:
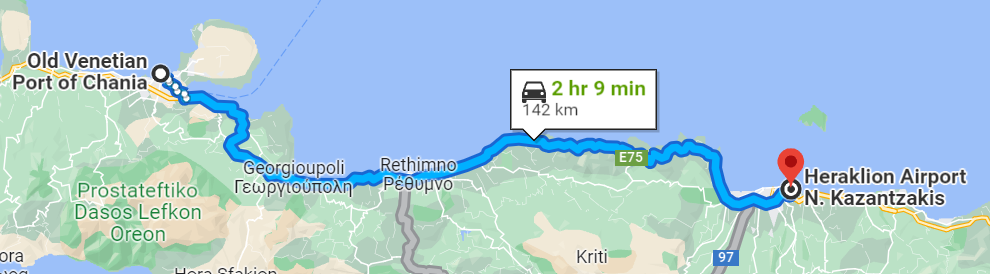
And this confirms that HEXA{Heraklion International Airport Nikos Kazantzakis} is the place we are
looking for.
Sovereign city
We intercepted a new message from « action man » sent days ago: « We will land at way
646940106, then we plan to hide near node 1803847939. Before we leave the city, we
will change our car near way 22762642. After that, relation 8810294 will allow us
to leave the city by staying on the left lane. » Find where they were hiding and
the city they are heading to.Format: Hexa{neighborhood_cityname}
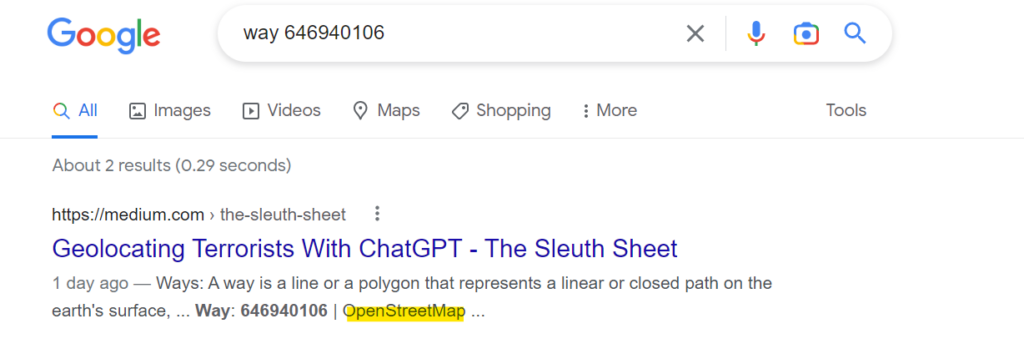
This message is talking about ways, nodes, and relations with identifiers. By using dorks: « way 646940106 »
we find out that those are keywords used in OpenStreetMap.
Using OpenStreetMap, we can have the method to get a node URL using « ? » button:
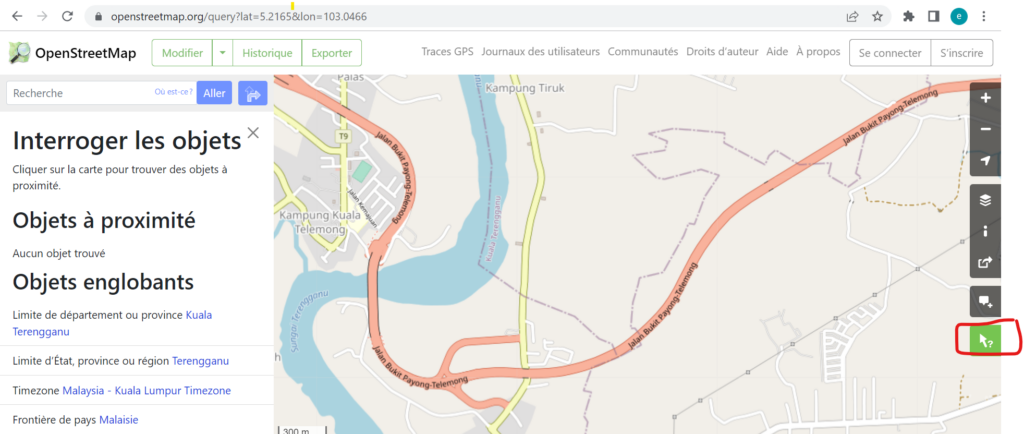
Once clicked on a random area, it gives nodes/ways/relations URL:
- https://www.openstreetmap.org/node/id
- https://www.openstreetmap.org/way/id
- https://www.openstreetmap.org/relation/id
Let us locate each one of them to retrace their route and find that they are heading to. The trick to locate the
city where they heading to is to get the relation, see that there is a « no turn left », so you continue forward, and
keep the left lane until you get on the highway to HEXA{Hougang Johor Bahru}.
Once this challenge is solved, two new challenges are unlocked: Original and Final Countdown.
Original
We contacted Interpol about « action man ». They have a biography record about him,
but it seems something erased and rewrote the biography report several times.
Forensics team managed to recover 12 different files but could not determine which
one was written by a human…Format: HEXA{report_number} Example: HEXA{13}
WARNING: You have only one try to get the right answer
No more GEOINT here. We must analyze some reports to identify the right one. The first step is analyzing
what we know. In the Bonbon challenge, we know that Another message with a picture was received
from ‘action man’. The attached message is in English, which gives us an information about Oleg’s Spoken
languages: at least English… Only 4 reports mention that Oleg speaks English (3, 5, 8, 12). So only one of these
reports could be the good one.
It is said in the challenge statement that you need to find the report that was written by a human. Implicitly,
others must have been generated by AI. Looking at creation date of each file allow us to see 2022-11-30,
which is the release date of Chat GPT, allowing to guess which AI was used to generate these reports.
We will use a tool to determine if the reports have been written by ChatGPT. If we try with
https://writer.com/ai-content-detector/ , it gives us the following results:
- 3 => 39%
- 5 => 84%
- 8 => 91% (real report)
- 12 => 73%
The error margin seems high, let us try another one. https://openai-openai-detector.hf.space/ gives us the
following results:
- 3 => 0,03%
- 5 => 0,02%
- 8 => 99,49%
Now it is pretty sure that HEXA{8} is the report we are looking for.
Final Countdown
We just received another message from « action man » sent on the phone we found at
the safehouse: « As planned, we are hiding in the building in zone 4. The religious
man waited us there as planned. This is not very secure, but it will do the job.
We not stay there more than a week, so find us a boat to reach the final location.
We will not be able to reach the sea on foot from there (more than three
kilometers by foot is more than the package can handle), so find us a car too… I
expect news in a couple days. I walked for five minutes and I arrived at a field
where locals were playing soccer. I talked with them and with some financial
incentive, they will warn me if they see or hear anything that could compromise
our position. » This is a great opportunity to find where they are hiding. We have
a chance to catch them, so give us the node OSM identifier of this « building » so
we can send a team.Format: HEXA{osm_identifier}
The first thing is: what is zone 4? At this point either we do not understand this, and we can’t solve this
challenge for now. Or we found the zones.kmz file on the mastermind website. This file can be found once challenge Herbaceous has been solved.
Once we have the file, we can figure out that zone 4 is a zone close to Kuala Terengganu in Malaysia, by using
a tool like https://master-branch-opensphere-ngageoint.surge.sh/. Now we are looking for a place in this
zone matching the following criteria:
- A religious man in a building, which means that the building is a place of worship ;
- A pitch where we can play soccer 5 minutes’ walk. At 1m/s speed it’s about 300 meters ;
- More than three kilometers from the sea.
Using overpass-turbo with the following query not taking the sea criteria into account:
[out:json][timeout:25];
(
nwr[« amenity »= »place_of_worship »]({{bbox}});
)->.place_of_worships;
(
nwr[« leisure »= »pitch »][« sport »= »soccer »]({{bbox}});
)->.soccer_fields;
(
nwr.place_of_worships(around.soccer_fields:300);
)->.place_of_worshipsNearSoccerfields
(.place_of_worshipsNearSoccerfields;);
out body;
>;
out skel qt;
only two results are provided:
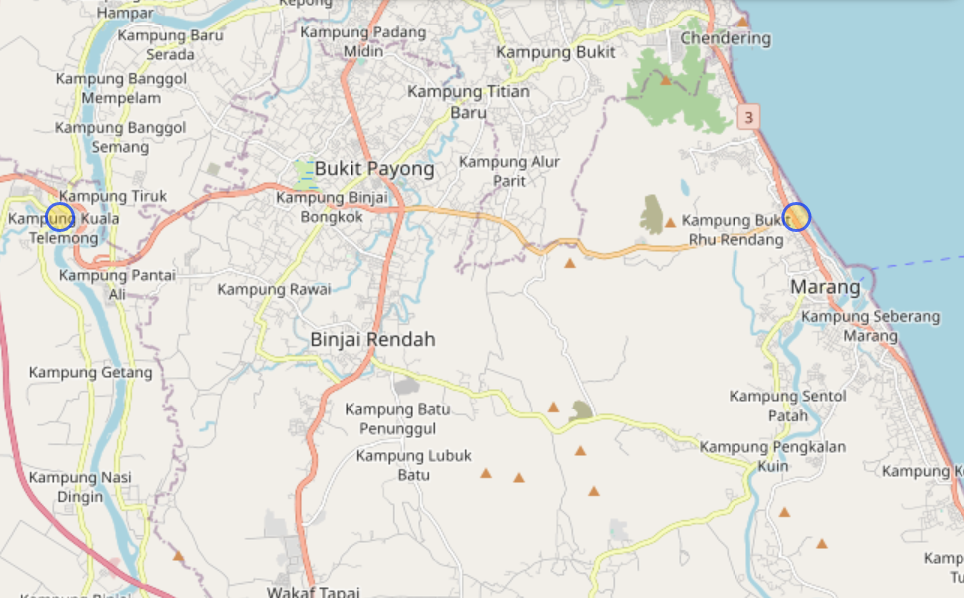
And only one is more than three kilometers from the sea. Clicking on the circle gives the asked OSM identifier
HEXA{3975813161}.
Several teams found other ways to get other places that matches full criteria, we agreed to add them as a
valid flag.